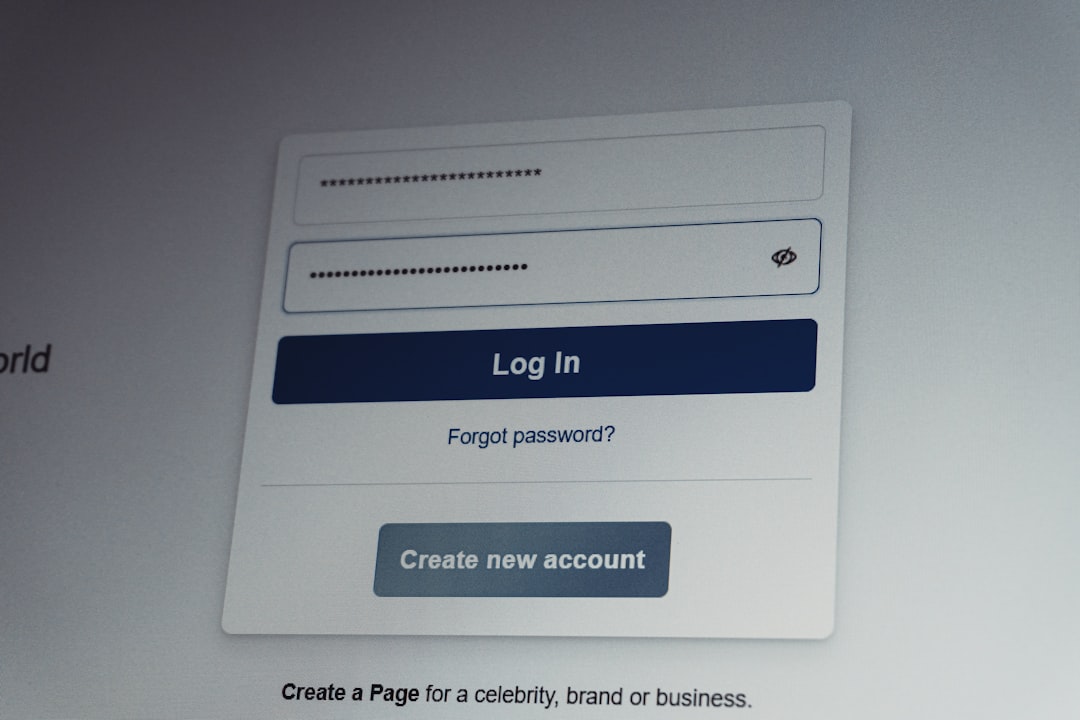
Credential Stuffing: How Attackers Use Stolen Passwords and How to Stop Them
Credential Stuffing: How Attackers Use Stolen Passwords and How to Stop Them Bottom Line Up Front Credential stuffing is an automated cyberattack where threat actors use lists of stolen username-password combinations to gain unauthorized access to user accounts across multiple services. Unlike brute force attacks that guess passwords, credential stuffing exploits the reality that users … Read more