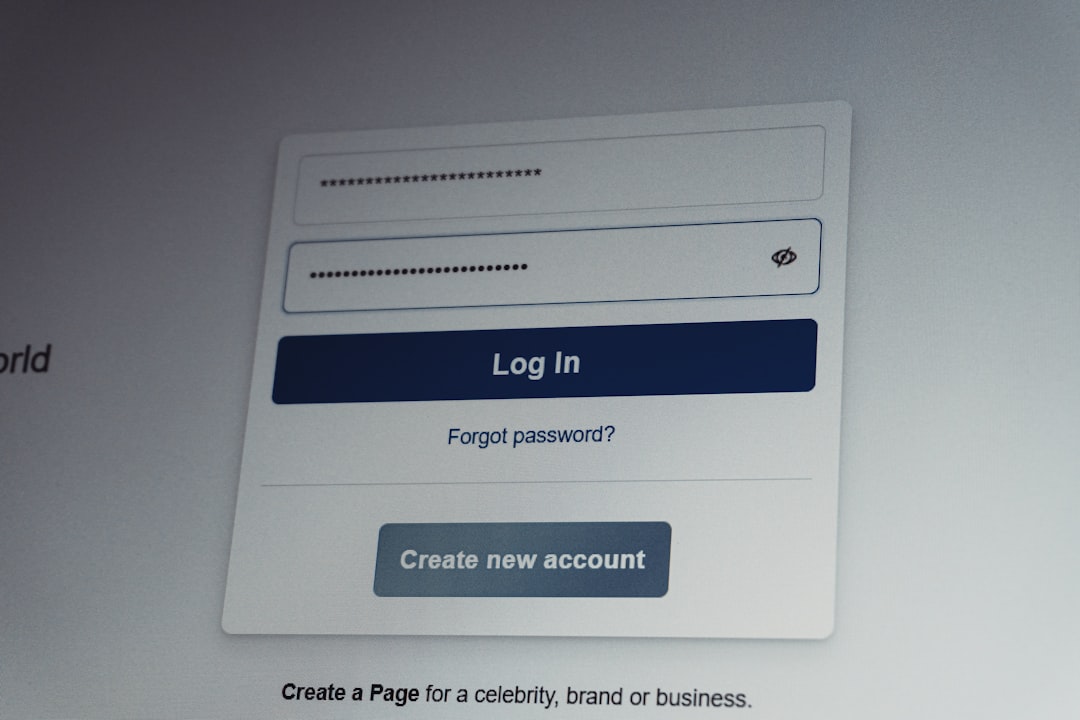
Phishing Simulation Programs: Testing Your Employees’ Awareness
Phishing Simulation Programs: Testing Your Employees’ Awareness Bottom Line Up Front A well-executed phishing simulation program transforms your employees from your biggest security vulnerability into your strongest defense. This guide walks you through building a program that reduces successful phishing attacks by 60-80% while satisfying compliance requirements for SOC 2, ISO 27001, NIST CSF, and … Read more