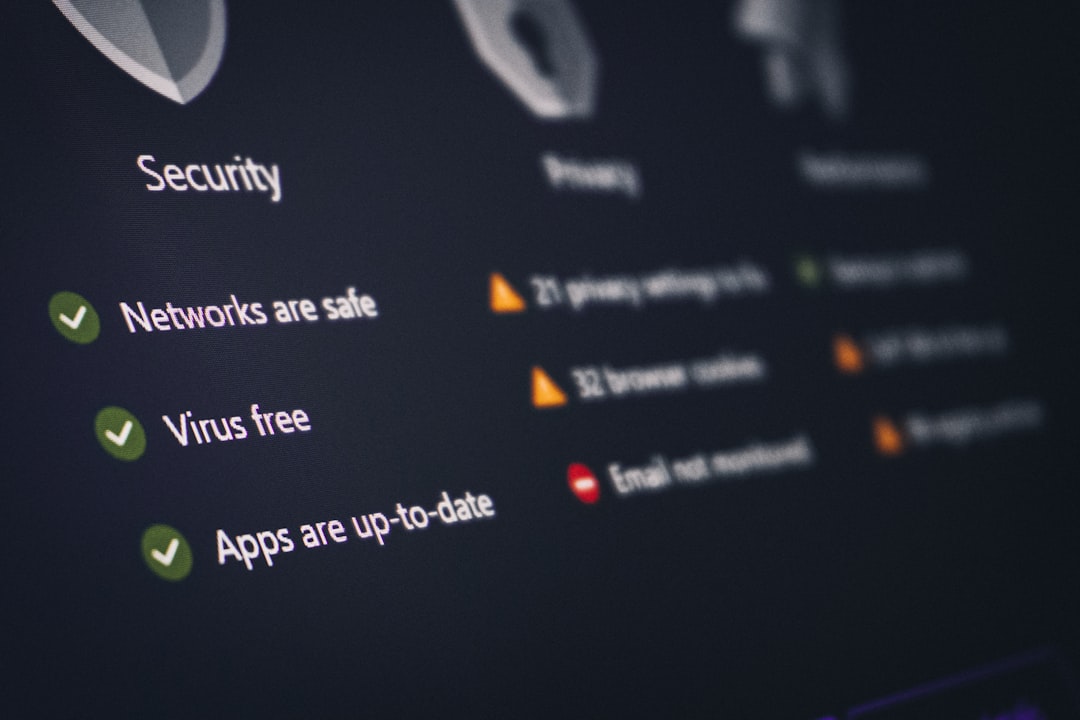
Best EDR Tools: Endpoint Detection and Response Platform Comparison
Best EDR Tools: Endpoint Detection and Response Platform Comparison Bottom Line Up Front EDR tools are your security program’s frontline defense against advanced threats that signature-based antivirus misses. If you’re managing more than 20 endpoints, handling sensitive data, or pursuing SOC 2 certification, you’ve outgrown basic endpoint protection. EDR platforms provide the behavioral monitoring, threat … Read more